Bob Dylan awarded France’s Legion of Honor
(Please consider making even a small contribution to the Welcome to Pottersville2 Quarterly Fundraiser happening now ($5.00 is suggested for those on a tight budget) or sending a link to your friends if you think the subjects discussed here are worth publicizing. Thank you for your support. We really appreciate it. Anything you can do will make a huge difference in this blog's ability to survive in these difficult economic times.)
One of the greats. A fearless spokeswoman for the ignored and abused. Has passed away.
Doris Lessing, any of whose 55 works of fiction merited prizes for courage, has disappeared from the comment scene where she illuminated controversial issues for 60 years. Long live Doris' spirit!
Doris Lessing, 88, holds flowers on her doorstep after learning she had been awarded the 2007 Nobel Prize in Literature. (Shaun Curry / AFP/Getty Images)
From Reuters: The novelist Doris Lessing, who tackled race, ideology, gender politics and the workings of the psyche in a prolific and often iconoclastic career, died in London on Sunday at the age of 94, her publisher HarperCollins said.
The British-Indian novelist Salman Rushdie hailed the "warmth, sharp mind and ferocity" of a writer who continually reinvented herself to challenge conventions . . . .
Born in what was then Persia, now Iran, on October 22, 1919, Lessing was raised in Southern Rhodesia, now Zimbabwe.
Lessing left school at 13, educating herself by reading Dickens, Tolstoy, D.H. Lawrence and Dostoyevsky but also living close to the land.
The trick today is - no one is supposed to know the facts. Thus, making their jobs so much easier.
Someone (lots of someones preferably) has to step in for Doris (and all the other courageous reporters) to document what the facts (and threats) are now. And what "intelligence" really means.
One look at Endgame’s product line explains a lot about their wariness. Their premier software, “Bonesaw,” shows what a powerful asset the corporation has become to America’s intelligence agencies.
Bonesaw is a targeting application that tracks servers and routers around the world. It maps out all the hardware attached to the Internet. Through these access points, NSA and Cyber Command can hack into or launch attacks against adversaries. The Bonesaw program functions essentially as a user-friendly map.
That map has at its disposal the geolocation and Internet address of every device connected to the Internet around the globe. By designating a country and city — like Beijing, China for example — and the name or address of a target — say, a People’s Liberation Army research facility — a user can find out what software is running on all of the computers inside the facility, what entry points to those computers exist, and a menu of custom exploits that can be used to sneak in.
We don't really need to know exactly what Michael Hastings had uncovered, do we? Or Barrett Brown? Or even the Snowman? My thoughts upon hearing of his defection were that if he were an NSA plant, the government boys would certainly have released some interesting data in order at least to prove his bona fides (and who could argue with learning even that little bit?)
From the fearless reporters at WhoWhatWhy.com we learn the juicy insiders' details on where our commissariat is leading US.
Deep Background
When the FBI raided the Dallas home of journalist Barrett Brown in March 2012, the travails of the Vanity Fair and Guardian contributor didn’t get much ink — that is, until Michael Hastings published an exclusive on the Brown raid on Buzzfeed.
The story included a copy of the search warrant that revealed why the government was so interested in Brown: Along with colleagues at the research wiki he started, ProjectPM (PPM), Brown was looking into a legion of shadowy cybersecurity firms whose work for the government raised all sorts of questions about privacy and the rule of law.
Since Hastings was familiar with the government contractors listed in the search warrant, he was also potentially culpable in whatever “crimes” the feds believed Brown and PPM were guilty of. Is this why he was being investigated in the days before his fatal crash on June 18, 2013? By then, Hastings had established a reputation as a fearless muckraker, whose stories often stripped the haloes from the powerful and well-connected:
- The besmirched “runaway” Special Forces general Stanley McChrystal, whose career Hastings had dispatched in a 2010 article for Rolling Stone
- The saintly General “King” David Petraeus — former commander of Central Command (CENTCOM), International Security Assistance Forces (ISAF) in Afghanistan, and head of the Central Intelligence Agency (CIA)
- Daniel Saunders — a former assistant US attorney for the Central District of California
- Former Secretary of State and presidential hopeful Hillary Clinton, with whose staff Michael had many pointed exchanges regarding State’s Benghazi spin.
“To Maintain and Cultivate an Enemies List”
In his profile on the blogging consortium True/Slant, Hastings confided that his “secret ambition” was “to maintain and cultivate an enemies list.” Such ironic distancing was Hastings’s way of making palatable an inherently cynical view of the world. He knew that power corrupted, and to effect change it was necessary to point out the Emperor’s glaringly naked flesh.
In this manner, he was much like his blogging colleague at True/Slant, Barrett Brown. So much so, in fact, that the latter approached Hastings to work on a project that would change the way the public viewed the murky world of intelligence contracting in the post-9/11 era.
For those unfamiliar with Brown’s tale, WhoWhatWhy has been chronicling his trials since February 2013. He is currently in federal custody in Ft. Worth, Texas, facing over a hundred years behind bars for researching 70,000 hacked emails obtained from the cybersecurity firm HBGary Federal and its parent company HBGary.
At no point is the government alleging he was involved in the hack itself. His putative “crime” is doing what investigative reporters are supposed to do: digging for the truth about breaches of the public trust.
To do this, Brown pioneered a collaborative wiki where researchers and journalists could sift through these emails and create an encyclopedia from the information contained within. This was known as ProjectPM (PPM).
In 2009, Brown invited Hastings to join forces on PPM, but Hastings’s interest was tempered by other commitments. When the two spoke next, Hastings told Brown he was working on something big.
“Not One of Us”
Hastings was referring to his impending 2010 article, “The Runaway General,” for Rolling Stone, in which he quoted several high-ranking military officials from within Gen. McChrystal’s inner circle disparaging their civilian command. The article caused a stir in official Washington, and eventually led to McChrystal being relieved of duty by President Obama.
Amid the fallout from this journalistic coup, an interesting narrative began forming in certain sectors of the press: “Michael Hastings is not one of us.” Hastings had broken one of the rules governing Washington’s hermetic circle of “access journalism” by quoting his subjects without their express permission. Elsewhere, most working reporters would call this, well, journalism.
Brown was quick to defend Hastings, penning an article for Vanity Fair titled, “Why The Hacks Hate Michael Hastings.” Later, the two blurbed each other’s books, further cementing their professional relationship.
One thing they shared was a deep discontent with the mainstream media. Indeed, Brown says, they were “obsessed with coming up with ways to change the dynamic.”
The busy Hastings never fully immersed himself in the work of PPM. “[Hastings] was an outlet for us to pass things to,” says Alan Ross, better known on PPM’s Internet relay chat (IRC) as Morpeth. “His relationship was one of talking to Barrett in my experience, rather than direct involvement in PPM.” He was “more of an associate than a member.”
“Get ready for your mind to be blown.”
For Hastings, Brown was clearly a confidential source — the type that flourishes best when kept in the dark and away from other reporters. Yet on January 24, 2013, Hastings tweeted that he was finally beginning to work on the Brown story, telling his interlocutors to “get ready for your mind to be blown.”
Kevin Gallagher, the administrator of Brown’s legal defense fund at FreeBarrettBrown.org, said Brown and Hastings hadn’t been able to talk securely in eight or nine months, but that after a few months of back and forth with Brown’s lawyers Hastings finally planned on interviewing him in custody in June.
After whistleblower Snowden’s bombshell revelations of dragnet surveillance by the National Security Agency (NSA), Hastings wrote an article on June 7 that referenced Brown for the first time since April 2012. Titled “Why Democrats Love To Spy On Americans,” it lambasted supposedly liberal Democrats for their Bush-like surveillance fixation and their unrelenting war on those who seek to expose the operations of the surveillance state:
“Transparency supporters, whistleblowers, and investigative reporters, especially those writers who have aggressively pursued the connections between the corporate defense industry and federal and local authorities involved in domestic surveillance, have been viciously attacked by the Obama administration and its allies in the FBI and DOJ.
[snip]
Barrett Brown, another investigative journalist who has written for Vanity Fair, among others [sic] publications, exposed the connections between the private contracting firm HB Gary (a government contracting firm that, incidentally, proposed a plan to spy on and ruin the reputation of the Guardian’s [Glenn] Greenwald) and who is currently sitting in a Texas prison on trumped up FBI charges regarding his legitimate reportorial inquiry into the political collective known sometimes as Anonymous.”
The article ended with “Perhaps more information will soon be forthcoming.”
The fact that he planned to interview Brown was corroborated by documentarian Vivien Weisman, who told WhoWhatWhy that she spoke to Hastings about it at a Los Angeles book signing for “Dirty Wars” in May 2013. And the editor of Buzzfeed reportedly confirmed that Hastings was in the midst of working on the Brown expose at the time of his death.
Knowing this prompts the question: what angle of the PPM research was Hastings about to tackle?
The evidence seems to point to another shadowy project revealed in the cache of hacked emails that PPM was sifting through: Romas/COIN.
Your Data Is Mine
Gallagher, who was briefed on the last discussion Hastings had with Brown before the planned interview, says, “Hastings had specifically asked about Romas/COIN.”
Romas/COIN was the name given to a program through which the U.S had been conducting “a secretive and immensely sophisticated campaign of mass surveillance and data mining against the Arab world,” according to emails hacked from the cybersecurity firm HBGary Federal.
Evidently, this program allows the intelligence community to “monitor the habits, conversations, and activity of millions of individuals at once.”
ProjectPM logo
Over the course of a year, Aaron Barr, CEO of HBGary Federal, sought out various companies to form a consortium that could wrest control of Romas/COIN from the current contract holder, Northrop Grumman. Eventually the consortium included no less than 12 different firms — ranging from niche software companies to behemoths like Google, Apple, and even Disney.
From the emails, it’s clear that “mobile phone software and applications constitute a major component of the program,” concludes the entry in ProjectPM. Periodic references to “semantic analysis,” “Latent Semantic Indexing,” and “specialized linguistics” indicate that the government agency overseeing the contract was clearly interested in automated dissection of spoken or written communication. This is the hallmark of NSA surveillance.
Is it possible that this consortium planned on developing mobile phone software and applications with bugs that would allow the US government to hack into targets’ phones and give it access to all of the communications within?
As detailed by New York Times national security reporter Mark Mazzetti, mobile phone intrusion has been par for the course in the military’s signals intelligence work abroad.
Checkmate
Claims of government surveillance capabilities embedded in private-company software are bolstered by recent reporting on the sale of “zero-day exploits” to government agencies.
“Zero-day exploits” refer to security vulnerabilities that are taken advantage of before the vulnerability becomes publicly known. As the jargon implies, there are zero days between the time the hole is discovered and the initial attack.
Endgame Systems, one such company cashing in on this new market, was of particular interest to Brown and ProjectPM. Deep in the cache of Aaron Barr’s emails are indications of just how secret the work of Endgame is.
In an email to employee John Farrell, then-Endgame CEO Chris Rouland states: “Please let HBgary know we don’t ever want to see our name in a press release.”
Farrell forwarded that note to Barr with the following explanation:
“Chris wanted me to pass this along. We’ve been very careful NOT to have public face on our company. Please ensure Palantir and your other partners understand we’re purposefully trying to maintain a very low profile. Chris [Rouland] is very cautious based on feedback we’ve received from our government clients. If you want to reconsider working with us based on this, we fully understand.”
One look at Endgame’s product line explains a lot about their wariness. Their premier software, “Bonesaw,” shows what a powerful asset the corporation has become to America’s intelligence agencies.
Bonesaw is a targeting application that tracks servers and routers around the world. It maps out all the hardware attached to the Internet. Through these access points, NSA and Cyber Command can hack into or launch attacks against adversaries. The Bonesaw program functions essentially as a user-friendly map.
That map has at its disposal the geolocation and Internet address of every device connected to the Internet around the globe. By designating a country and city — like Beijing, China for example — and the name or address of a target — say, a People’s Liberation Army research facility — a user can find out what software is running on all of the computers inside the facility, what entry points to those computers exist, and a menu of custom exploits that can be used to sneak in.
Sock Puppets and Other Tricks
Other clues as to what ProjectPM-related material may have led the FBI to investigate Michael Hastings can be found in his published work.
Endgame Systems CEO Nathaniel Fick. Formerly of the Center for a New American Security, Fick took over for Endgame in November 2012.
In a May 18, 2012, article on propaganda efforts by the State Department, Hastings referred to a “program being developed by the Pentagon [that] would design software to create “sock puppets” on social media outlets.” The HBGary emails are littered with references to this type of “persona management” technology.
Principal among these was a June 2010 United States Air Force (USAF) contract from the 6th Contracting Squadron at MacDill Air Force Base in Florida. It sought providers of “persona management software” that would allow 50 users to control up to 500 fictional personae.
These sock puppets were required to be “replete with background, history, supporting details, and cyber presences that are technically, culturally, and geographically consistent.” In other words, avatars so convincing they could fool the people with whom they were interacting into believing they were real.
MacDill Air Force Base is home to the United States Special Operations Command (USSOCOM), the section of the military that oversees and coordinates all special-forces activity globally. USSOCOM lists under its “core activities” the employment of psychological operations (PSYOPS) and information operations (IO) — exactly the type of activity this “sockpuppeting” technology would be employed in.
To put it another way: a clone army for future psywars.
Gone With The Mercedes
Given the information currently available it is impossible to know with certainty what angle in the Brown case Michael Hastings was pursuing at the time of his death.
But Hastings’s credibility and national security contacts would have served him well in digging deeper into ProjectPM’s cache of hacked emails, perhaps exposing to the light of public scrutiny other secretive government contractors in the manner that Brown had begun. (See the “Team Themis” affair.)
With that potential suddenly snuffed out, it’s not surprising the Internet is abuzz with speculation over Hastings’s death. We’ve contributed to the investigation surrounding it but, with so few hard facts at hand, now is not the time to speculate about whether foul play was involved. What’s clear is that an important voice in the grand tradition of investigative journalism has been silenced.
Hopefully, more information will come to light, and we will know with a fair degree of certainty what Michael Hastings was working on that attracted the government’s watchful eye. That is, unless all of his information was incinerated with him in the early hours of that June morning.
Jeremy Hammond Gets 10 Years In Prison For an Act Of Nonviolence
Good morning. Thank you for this opportunity. My name is Jeremy Hammond and I’m here to be sentenced for hacking activities carried out during my involvement with Anonymous. I have been locked up at MCC for the past 20 months and have had a lot of time to think about how I would explain my actions.
Before I begin, I want to take a moment to recognize the work of the people who have supported me. I want to thank all the lawyers and others who worked on my case:
Elizabeth Fink, Susan Kellman, Sarah Kunstler, Emily Kunstler, Margaret Kunstler, and Grainne O’Neill. I also want to thank the National Lawyers Guild, the Jeremy Hammond Defense Committee and Support Network, Free Anons, the Anonymous Solidarity Network, Anarchist Black Cross, and all others who have helped me by writing a letter of support, sending me letters, attending my court dates, and spreading the word about my case. I also want to shout out my brothers and sisters behind bars and those who are still out there fighting the power.
The acts of civil disobedience and direct action that I am being sentenced for today are in line with the principles of community and equality that have guided my life. I hacked into dozens of high profile corporations and government institutions, understanding very clearly that what I was doing was against the law, and that my actions could land me back in federal prison. But I felt that I had an obligation to use my skills to expose and confront injustice—and to bring the truth to light.
Could I have achieved the same goals through legal means? I have tried everything from voting petitions to peaceful protest and have found that those in power do not want the truth to be exposed. When we speak truth to power we are ignored at best and brutally suppressed at worst. We are confronting a power structure that does not respect its own system of checks and balances, never mind the rights of it’s own citizens or the international community.
My introduction to politics was when George W. Bush stole the Presidential election in 2000, then took advantage of the waves of racism and patriotism after 9/11 to launch unprovoked imperialist wars against Iraq and Afghanistan. I took to the streets in protest naively believing our voices would be heard in Washington and we could stop the war.
Instead, we were labeled as traitors, beaten, and arrested.
I have been arrested for numerous acts of civil disobedience on the streets of Chicago, but it wasn’t until 2005 that I used my computer skills to break the law in political protest. I was arrested by the FBI for hacking into the computer systems of a right-wing, pro-war group called Protest Warrior, an organization that sold racist t-shirts on their website and harassed anti-war groups. I was charged under the Computer Fraud and Abuse Act, and the “intended loss” in my case was arbitrarily calculated by multiplying the 5000 credit cards in Protest Warrior’s database by $500, resulting in a total of $2.5 million. My sentencing guidelines were calculated on the basis of this “loss,” even though not a single credit card was used or distributed – by me or anyone else. I was sentenced to two years in prison.
While in prison I have seen for myself the ugly reality of how the criminal justice system destroys the lives of the millions of people held captive behind bars. The experience solidified my opposition to repressive forms of power and the importance of standing up for what you believe.
When I was released, I was eager to continue my involvement in struggles for social change. I didn’t want to go back to prison, so I focused on above-ground community organizing. But over time, I became frustrated with the limitations, of peaceful protest, seeing it as reformist and ineffective. The Obama administration continued the wars in Iraq and Afghanistan, escalated the use of drones, and failed to close Guantanamo Bay.
Around this time, I was following the work of groups like Wikileaks and Anonymous. It was very inspiring to see the ideas of hactivism coming to fruition. I was particularly moved by the heroic actions of Chelsea Manning, who had exposed the atrocities committed by U.S. forces in Iraq and Afghanistan. She took an enormous personal risk to leak this information – believing that the public had a right to know and hoping that her disclosures would be a positive step to end these abuses. It is heart-wrenching to hear about her cruel treatment in military lockup.
I thought long and hard about choosing this path again. I had to ask myself, if Chelsea Manning fell into the abysmal nightmare of prison fighting for the truth, could I in good conscience do any less, if I was able? I thought the best way to demonstrate solidarity was to continue the work of exposing and confronting corruption.
I was drawn to Anonymous because I believe in autonomous, decentralized direct action. At the time Anonymous was involved in operations in support of the Arab Spring uprisings, against censorship, and in defense of Wikileaks. I had a lot to contribute, including technical skills, and how to better articulate ideas and goals. It was an exciting time – the birth of a digital dissent movement, where the definitions and capabilities of hacktivism were being shaped.
I was especially interested in the work of the hackers of LulzSec who were breaking into some significant targets and becoming increasingly political. Around this time, I first started talking to Sabu, who was very open about the hacks he supposedly committed, and was encouraging hackers to unite and attack major government and corporate systems under the banner of Anti Security. But very early in my involvement, the other Lulzsec hackers were arrested, leaving me to break into systems and write press releases. Later, I would learn that Sabu had been the first one arrested, and that the entire time I was talking to him he was an FBI informant.
Anonymous was also involved in the early stages of Occupy Wall Street. I was regularly participating on the streets as part of Occupy Chicago and was very excited to see a worldwide mass movement against the injustices of capitalism and racism. In several short months, the “Occupations” came to an end, closed by police crackdowns and mass arrests of protestors who were kicked out of their own public parks. The repression of Anonymous and the Occupy Movement set the tone for Antisec in the following months – the majority of our hacks against police targets were in retaliation for the arrests of our comrades.
I targeted law enforcement systems because of the racism and inequality with which the criminal law is enforced. I targeted the manufacturers and distributors of military and police equipment who profit from weaponry used to advance U.S. political and economic interests abroad and to repress people at home. I targeted information security firms because they work in secret to protect government and corporate interests at the expense of individual rights, undermining and discrediting activists, journalists and other truth seekers, and spreading disinformation.
I had never even heard of Stratfor until Sabu brought it to my attention. Sabu was encouraging people to invade systems, and helping to strategize and facilitate attacks. He even provided me with vulnerabilities of targets passed on by other hackers, so it came as a great surprise when I learned that Sabu had been working with the FBI the entire time.
On December 4, 2011, Sabu was approached by another hacker who had already broken into Stratfor’s credit card database. Sabu, under the watchful eye of his government handlers, then brought the hack to Antisec by inviting this hacker to our private chatroom, where he supplied download links to the full credit card database as well as the initial vulnerability access point to Stratfor’s systems.
I spent some time researching Stratfor and reviewing the information we were given, and decided that their activities and client base made them a deserving target. I did find it ironic that Stratfor’s wealthy and powerful customer base had their credit cards used to donate to humanitarian organizations, but my main role in the attack was to retrieve Stratfor’s private email spools which is where all the dirty secrets are typically found.
It took me more than a week to gain further access into Stratfor’s internal systems, but I eventually broke into their mail server. There was so much information, we needed several servers of our own in order to transfer the emails. Sabu, who was involved with the operation at every step, offered a server, which was provided and monitored by the FBI. Over the next weeks, the emails were transferred, the credit cards were used for donations, and Stratfor’s systems were defaced and destroyed. Why the FBI would introduce us to the hacker who found the initial vulnerability and allow this hack to continue remains a mystery.
As a result of the Stratfor hack, some of the dangers of the unregulated private intelligence industry are now known. It has been revealed through Wikileaks and other journalists around the world that Stratfor maintained a worldwide network of informants that they used to engage in intrusive and possibly illegal surveillance activities on behalf of large multinational corporations.
After Stratfor, I continued to break into other targets, using a powerful “zero day exploit” allowing me administrator access to systems running the popular Plesk webhosting platform. Sabu asked me many times for access to this exploit, which I refused to give him. Without his own independent access, Sabu continued to supply me with lists of vulnerable targets. I broke into numerous websites he supplied, uploaded the stolen email accounts and databases onto Sabu’s FBI server, and handed over passwords and backdoors that enabled Sabu (and, by extension, his FBI handlers) to control these targets.
These intrusions, all of which were suggested by Sabu while cooperating with the FBI, affected thousands of domain names and consisted largely of foreign government websites, including those of XXXXXXX, XXXXXXXX, XXXX, XXXXXX, XXXXX, XXXXXXXX, XXXXXXX and the XXXXXX XXXXXXX. In one instance, Sabu and I provided access information to hackers who went on to deface and destroy many government websites in XXXXXX. I don’t know how other information I provided to him may have been used, but I think the government’s collection and use of this data needs to be investigated.
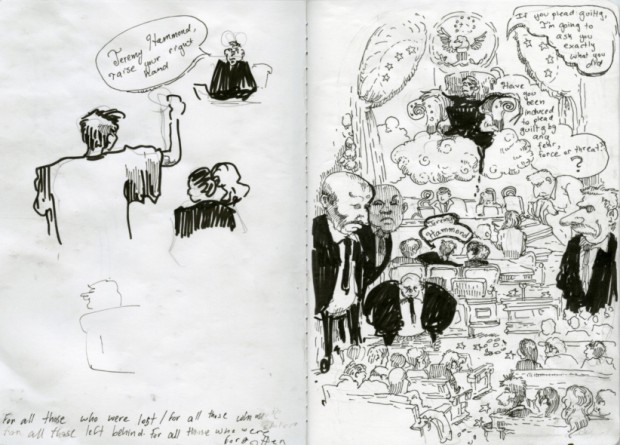
Sketch from inside Judge Preska’s courtroom by Molly Crabapple
The government celebrates my conviction and imprisonment, hoping that it will close the door on the full story. I took responsibility for my actions, by pleading guilty, but when will the government be made to answer for its crimes?
The U.S. hypes the threat of hackers in order to justify the multi billion dollar cyber security industrial complex, but it is also responsible for the same conduct it aggressively prosecutes and claims to work to prevent. The hypocrisy of “law and order” and the injustices caused by capitalism cannot be cured by institutional reform but through civil disobedience and direct action. Yes I broke the law, but I believe that sometimes laws must be broken in order to make room for change.
In the immortal word of Frederick Douglas, “Power concedes nothing without a demand. It never did and it never will. Find out just what any people will quietly submit to and you have found out the exact measure of injustice and wrong which will be imposed upon them, and these will continue till they are resisted with either words or blows, or both. The limits of tyrants are prescribed by the endurance of those whom they oppress.”
This is not to say that I do not have any regrets. I realize that I released the personal information of innocent people who had nothing to do with the operations of the institutions I targeted. I apologize for the release of data that was harmful to individuals and irrelevant to my goals. I believe in the individual right to privacy – from government surveillance, and from actors like myself, and I appreciate the irony of my own involvement in the trampling of these rights. I am committed to working to make this world a better place for all of us. I still believe in the importance of hactivism as a form of civil disobedience, but it is time for me to move on to other ways of seeking change.
My time in prison has taken a toll on my family, friends, and community. I know I am needed at home. I recognize that 7 years ago I stood before a different federal judge, facing similar charges, but this does not lessen the sincerity of what I say to you today.
It has taken a lot for me to write this, to explain my actions, knowing that doing so — honestly — could cost me more years of my life in prison. I am aware that I could get as many as 10 years, but I hope that I do not, as I believe there is so much work to be done.
STAY STRONG AND KEEP STRUGGLING!To schedule interviews with Jeremy Hammond’s attorneys and supporters following today’s sentencing please contact Andy Stepanian,
631.291.3010, andy@sparrowmedia.net.
The Jeremy Hammond Defense Committee is a coalition of family members, activists, lawyers, and other supporters who are working together to protect free speech and to support Jeremy Hammond. The committee’s goal is to provide information to the public and the press, to organize events related to Jeremy’s case, and to support Jeremy while he is in jail. For more information, please visit http://freejeremy.net.
In memory of Christopher Hitchens who would not be surprised:



































No comments:
Post a Comment